#
API
2FAuth is built on top of its own REST API (following OpenAPI 3.1 specification), which can be used to make any other app communicate with 2FAuth.
The API provides endpoints to manage most of the 2FAuth resources:
#
Authentication
You authenticate in the 2FAuth API with a Personal Access Token (PAT) built upon the OAUTH Bearer authentication scheme (see RFC 6750).
That means the PAT has to be passed via the HTTP Authorization header in every request made to the API.
Authorization: Bearer eyJ0eXAiOiJKV1QiLCJhbGciOiJSUzI1NiJ9.eyJhdWQiOiIxIiwianRpIjoiMzZjOTc5NmFlZGI2OGQyYmE2YTIyMTE0NTNA PAT is valid until you decide to revoke it.
#
Creating an access token
Open the 2FAuth Settings > OAUTH section and click the Generate a new token link to generate a new token.
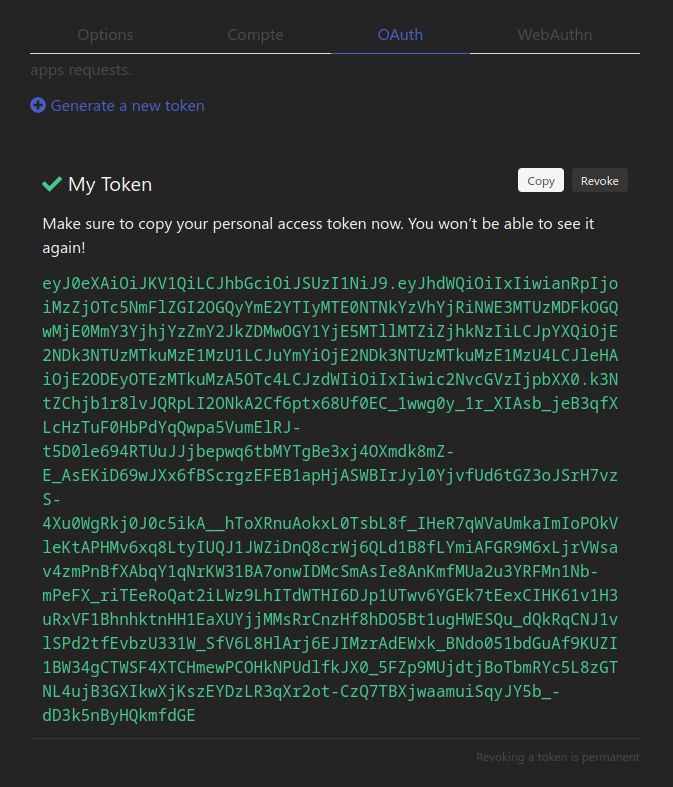
The token will only be shown once, right after its creation, so copy it immediately because you won't be able to display it again.
#
Revoking a token
You can revoke a personal access token by simply clicking its
Revoke
button in the Settings > OAUTH section. A request made with a revoked token will receive a 401 Unauthorized response.
The revocation of a token is permanent and cannot be undone.
#
API documentation
The API has its own dedicated documentation that you can browse in a lightweight format below.
You may also use the fullscreen format which provides previous versions, a more comfortable layout and modern features like advanced search, mocking and more: